Tech
How to Hide Pictures on Snapchat with My Eyes Only feature & More

Snapchat enhances the quality of any photos or selfies that we upload. This is mainly due to the features that are built into the app. These include filters, emojis and texts, as well as music. There are photos that we may want to keep hidden from other Snapchat users. Do you know how to hide photos on Snapchat? If you don’t, don’t worry. You can find all the information right here. Snapchat photos can be hidden using different methods. The steps will vary depending on the device that you use to browse Snapchat. Snapchat has amazing features such as Dark Mode, Premium Features, and more. Snapchat also has a feature that allows you to hide photos.
Read on to learn how to hide photos from Snapchat. Continue reading to learn how to hide photos saved on Snapchat. How to Hide Photos in Snapchat?
Hiding photos on Snapchat is easy. You can save them to your device. You can also hide photos on Snapchat by using the features available on the platform. This feature allows you to hide certain features from other users of the platform. Below, you can see the options that will hide your photo on Android and iPhone devices. You will also find detailed information on the Snapchat hidden folder and My Eyes Only feature.
How to Hide Photos On Snapchat Using the “My Eyes Only” Feature?
There are some simple steps to follow when you want the My Eyes Only option on Snapchat to hide photos. Follow the steps and you will be able to easily hide photos. Check out the steps right now.
1. Launch Snapchat from your device.
2. Log in to Your account.
3. Swipe the camera up and go to Memory.
4. Click on the snaps you want to hide.
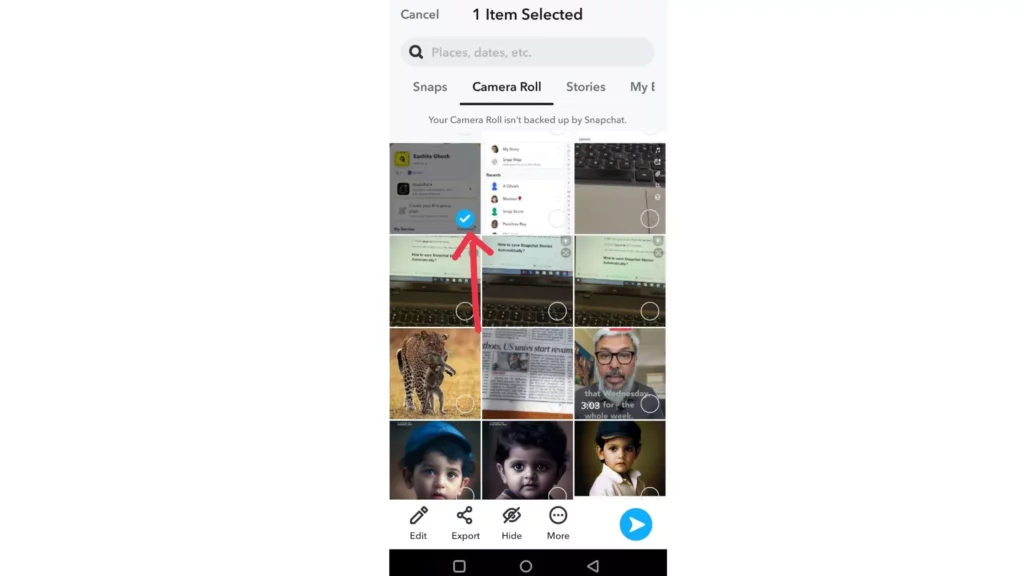
5. Click on the hide button at the bottom of the screen.
6. You can see the option Only me you get to see it.
7. Click on move.
With the My eyes only option, your snap will be hidden. Also, check out Want to Make a Snapchat filter? Try These 3 Simple Methods
Hide Photos on Snapchat through Saved Chat
There is a secret folder you can use to save photos to Snapchat. What is it? I know that the answer is yes. The secret folder’s name is Chatbox.
While anyone using your phone may want to check the“My Eyes Only”file, they will not be checking every Snapchat chat. It’s easy to hide photos in the Snapchat chatbox. Follow the steps below to learn more about Snapchat secrets.
Launch the Snapchat app.
2. Tap on the chat icon at the bottom of the screen.
3. Tap on the names of your Facebook friends.
4. Send a picture.
5. Tap and hold a photo, then click on save in a chat.
6. Click Chat Settings to access .
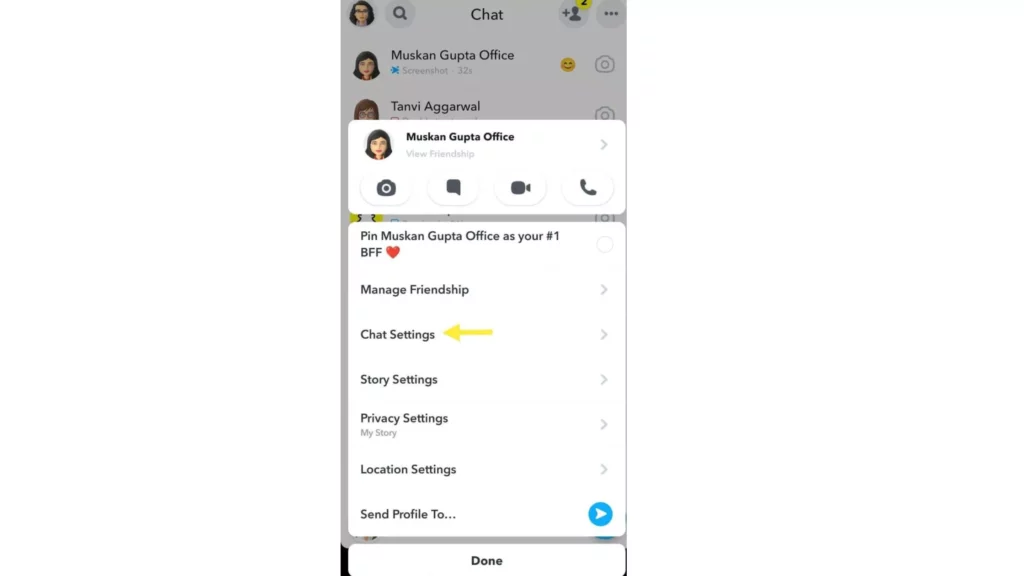
7. Click on Remove from Chat Feed to clear it.
8. Tap on to clear the conversation.
Note :- Saved Chat won’t delete your photos. It will be hidden in the chat.
You should send your photos only to someone you trust, such as your best friend, sibling or anyone else. Also, read How to Unblock Someone on Snapchat in 2022. Easy Steps
Downloading the Photos from the Saved Chat?
You can easily download the photos by following the steps below.
Launch the Snapchat application.
2. Click on the profile icon at the left of the screen.
3. On the profile page, click the my friends button.
4. Tap on to select a friend.
5. The saved chat will be displayed on the screen.
6. Tap and hold it on a photo.
7. Tap on to save to Camera Roll.
You can also read Are Snapchat Stories Public: A Wrapped Conundrum Decoded in 2023.
Read Are Snapchat Stories Public? A Wrapped Conundrum in 2023.
Learn how to Turn on the ‘My Eyes Only’ Feature on Snapchat.
If you want to use the My Eyes Only feature, you will need to follow these simple steps:
Launch Snapchat on your device.
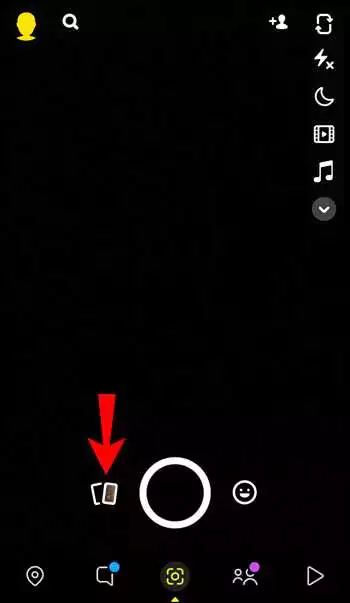
2. Swipe the camera to view all of your memories.
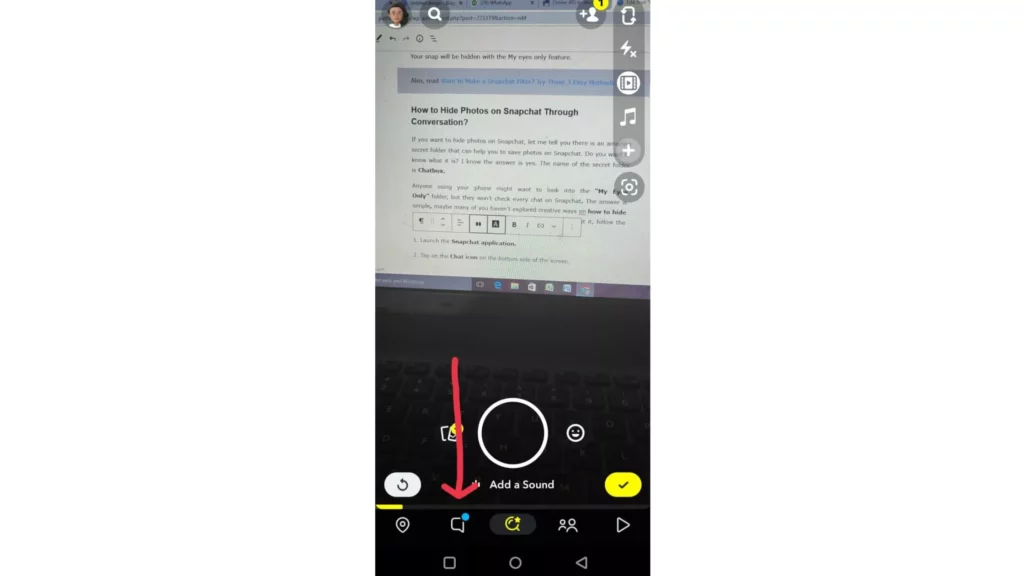
3. Click on the icon of the card located at the bottom right corner of the screen.
4. Click on the option “19459003” My Eyes Only.
5. Select Quick setup.
6. Enter the 4-digit password .
7. You should never lose your password for My Eyes Only. Otherwise, you will lose all the data you have saved. Hide Photos on SC (2022)
Wrapping Up
I hope the article helped you to understand how to hide photos on Snapchat with the help of the above-mentioned features. You can hide photos on both Android devices and iOS devices. Follow the steps exactly as they are described. Path of EX has all the latest information.
Frequently asked questions
1 How do you enable the My eyes only feature on Snapchat?
If you want to hide photos from Snapchat using the “My Eyes Only” feature, follow the steps below.
Launch Snapchat on your device.
2. Swipe the camera to view your photos.
3. Click on the card icon located at the bottom of your screen.
4. Click on the option My Eyes Only .
5. Select Quick setup.
6. Enter the 4-digit password .
7. Click on circle option and then select Continue.
2. How to hide photos using “My Eyes Only” on Snapchat?
To conceal photos on Snapchat, follow the steps below.
Launch Snapchat on your device.
2. Log in to your account .
3. Swipe the camera up to get to memories.
4. Click on the snaps you want to hide.
5. Click on the hide button at the bottom of the screen.
6. You can see the option Only me
6.
7. Click on to move.
3. How to hide photos from Snapchat in the chatbox (19659082)? Read the steps below to hide photos on Snapchat within the chatbox:
Launch the Snapchat application .
2. Tap on the chat icon at the bottom of the screen.
3. Tap on the names of your Facebook friends.
4. Send a picture.
5. Tap on Quick setup
6. Enter a 4 four-digit password.
7. Finally, press and hold the friends chat button.
8. Tap on to learn more.
9. Tap on to clear the conversation.
4. Why can’t i hide snaps with My Eyes Only?
You may not be able to hide snaps on My Eyes Only for the following reasons:
Forgotten My Eyes Only password.
2. Snapchat app is outdated.
3. Snapchat app has bugs/glitches.
4. Server issues.
5. How to enter My Eyes Only without losing anything on Snapchat?
If your goal is to not lose anything by using My Eyes Only Snapchat, you should follow these two methods:
You must select the option Alternate passcode instead of Forgot passcode.
2. Contact the Snapchat Support Team.
6. How to recover My Eyes Only photos on Snapchat?
My Eyes Only photos can be recovered using the following methods:
Change the My Eyes Only Passcode (19459029) 2. Snapshot Memories: Back up your photos
Submit your request to download your Snapchat Data.
7. How to view hidden photos on Snapchat? You can view the hidden photos in Snapchat using the My Eyes Only function.
Tech
Ultimate Guide to Protecting Yourself from Phishing Scams

Phishing is a malicious practice used by cybercriminals to deceive individuals into revealing sensitive information such as passwords, credit card details, or social security numbers. These scammers often masquerade as trustworthy entities, such as banks, government agencies, or popular online services, in an attempt to trick unsuspecting victims. Phishing attacks usually occur through email, text messages, or fake websites designed to look legitimate.
How Phishing Scams Work?
Phishing scams rely on social engineering techniques to manipulate victims into taking action. These scams typically start with an email or message that appears to be from a reputable source, urging the recipient to click on a link or provide personal information. The link often leads to a fraudulent website that mimics the legitimate one, tricking users into entering their login credentials or other sensitive data. Once the cybercriminals gain access to this information, they can use it for various malicious purposes, including identity theft, financial fraud, or unauthorized access to personal accounts.
Types of Phishing Scams
Phishing scams come in various forms, each with its objective and method of deception. Some common types of phishing scams include:
Email phishing: This is the most common form of phishing, where scammers send fraudulent emails disguised as legitimate organizations. These emails often contain urgent requests for personal information or ask users to click on malicious links.
Spear phishing: Unlike regular phishing attacks, spear phishing targets specific individuals or organizations. The scammers gather information about their targets to personalize the attack and make it more convincing.
Whaling: Whaling attacks specifically target high-profile individuals, such as CEOs or executives, to gain access to sensitive corporate information or financial assets.
Smishing: Smishing, or SMS phishing, involves sending fraudulent text messages that appear to be from trusted sources. These messages often contain links or requests for personal information.
Vishing: Vishing, or voice phishing, relies on phone calls to deceive victims into revealing sensitive information. Scammers may pose as bank representatives, government officials, or technical support personnel to gain the victim’s trust.
Signs of a Phishing Attack
Here are some common indicators that can help you identify a phishing attempt:
Sender’s email address: Pay close attention to the email address of the sender. Phishing emails often use domain names that are slightly different from the legitimate ones, such as “g00gle.com” instead of “google.com.”
Urgency or fear tactics: Phishing emails often create a sense of urgency or fear to prompt immediate action.
Poor grammar and spelling: Phishing emails often contain grammatical errors, spelling mistakes, or awkward phrasing.
Unsolicited requests for personal information: Legitimate organizations rarely ask for personal information via email or messages. Be skeptical of any unsolicited requests for passwords, credit card numbers, or social security numbers.
Suspicious URLs: Hover your mouse over any links in the email without clicking on them. If the link does not match the displayed text or leads to a suspicious website, it’s likely a phishing attempt.
Tips to Avoid Phishing Scams
Protecting yourself from phishing scams requires a combination of vigilance and awareness. Here are some tips to help you identify and avoid phishing scams:
Think before you click: Be cautious of any links or attachments in emails or messages, especially if they’re unsolicited or seem suspicious. Verify the legitimacy of the sender and the content before clicking on anything.
Double-check the sender: Verify the email address of the sender and look for any signs of it being a spoofed or fake address.
Be skeptical of urgent requests: Phishing emails often create a sense of urgency to manipulate victims. Take a step back and evaluate the situation critically
Don’t share personal information: Be cautious of providing personal information, such as passwords or social security numbers, via email or messages. Legitimate organizations have secure channels for such requests.
Keep your devices and software updated: Regularly update your operating system, web browsers, and security software to ensure you have the latest protections against phishing attacks.
Educate yourself: Stay informed about the latest phishing techniques and scams.
How to Protect Yourself from Phishing Scams?
Protecting yourself from phishing scams requires a proactive approach and the adoption of best practices for online security. Here are some effective measures to safeguard your personal information:
Use strong and unique passwords: Create complex passwords that include a combination of letters, numbers, and special characters. Avoid reusing passwords across multiple accounts to minimize the risk of compromise.
Enable two-factor authentication: Two-factor authentication adds an extra layer of security by requiring a secondary verification method, such as a fingerprint or a one-time code sent to your phone, when logging into an account.
Be cautious of sharing personal information online: Be mindful of the information you share on social media platforms and other online platforms. Cybercriminals can use this information to craft personalized phishing attacks.
Regularly update your antivirus software: Keep your antivirus software up to date to protect against the latest phishing threats. Antivirus software can help detect and block malicious websites and attachments.
Encrypt your sensitive data: Use encryption tools to protect your sensitive data, such as financial information or personal documents. Encryption ensures that even if your data is intercepted, it remains unreadable to unauthorized individuals.
Backup your data: Regularly backup your important files and documents to an external hard drive or cloud storage. In the event of a successful phishing attack, having backups ensures you can recover your data without paying a ransom.
Best Practices for Secure Online Behavior
In addition to protecting yourself from phishing scams, practicing secure online behavior can significantly reduce your risk of falling victim to cybercriminals. Here are some best practices to follow:
Keep your software updated: Regularly update your operating system, web browsers, and other software to ensure you have the latest security patches and bug fixes.
Use a firewall: Enable a firewall on your computer or network to monitor and block unauthorized access attempts.
Use a secure network: Avoid accessing sensitive information or conducting financial transactions while connected to public Wi-Fi networks. Use a virtual private network (VPN) when accessing the internet on untrusted networks.
Beware of suspicious downloads: Be cautious when downloading files from the internet, especially from unknown sources. Malicious software can often be disguised as legitimate files.
Regularly check your accounts: Periodically review your bank statements, credit card statements, and other financial accounts for any unauthorized transactions. Report any suspicious activity immediately.
Educate yourself and your family: Teach your family members, especially children, about the risks of phishing scams and the importance of online security. Encourage them to follow best practices and report any suspicious activity.
Enhance your Online Security
Several tools and technologies can significantly enhance your online security and protect you from phishing scams. Here are some recommended options:
Password managers: Password managers securely store and generate strong passwords for your various online accounts. They can also help detect and warn you of potential phishing websites.
Email filters: Enable strong spam filters on your email accounts to automatically detect and filter out phishing and spam emails.
Web browser security extensions: Install browser extensions that provide additional security features, such as anti-phishing protection and website reputation ratings.
Antivirus and anti-malware software: Invest in reputable antivirus and anti-malware software that can detect and block phishing attacks, malicious websites, and infected files.
Virtual private network (VPN): A VPN encrypts your internet connection, ensuring your online activities are secure and private. It can also help protect against phishing attempts on unsecured networks.
Final Thoughts!
Phishing scams continue to pose a significant threat to individuals and organizations alike. By understanding how these scams work, being vigilant for signs of phishing attempts, and adopting best practices for online security, you can protect yourself from falling victim to these cybercriminals. Remember to stay informed, educate yourself and others, and utilize the available tools and technologies to enhance your online security. By staying one step ahead of cybercriminals, you can safeguard your personal information and enjoy a safer online experience.
Tech
OpenAI Releases GPT 3.5 Turbo Instruct
OpenAI, a leading artificial intelligence (AI) research laboratory, has recently released its latest model, GPT-3.5 Turbo Instruct. This groundbreaking development has the potential to revolutionize the way we interact with AI systems and unlock new possibilities in various industries. In this article, we will delve into the capabilities of GPT-3.5 Turbo Instruct, understand how it differs from previous versions, explore its use cases, discuss the benefits and limitations, provide guidance on getting started, showcase successful implementations, touch upon the future of AI, and address ethical considerations.
Understanding Turbo Instruct GPT-3.5
Turbo Instruct GPT-3.5 is an advanced language model developed by OpenAI. It leverages the power of deep learning to generate human-like text based on the given prompts and instructions. This model boasts an impressive 175 billion parameters, enabling it to comprehend and generate highly sophisticated responses. With GPT-3.5 Turbo Instruct, users can communicate with AI systems more naturally and intuitively, making it a game-changer for a wide range of applications. The capabilities of GPT-3.5 Turbo Instruct extend beyond simple text completion. It can understand and follow detailed instructions, assisting users in complex tasks such as coding, writing, translation, and more. Whether it’s generating code snippets, drafting emails, or even creating conversational agents, GPT-3.5 Turbo Instruct can provide valuable assistance by generating high-quality content that aligns with user instructions.
How GPT-3.5 Turbo Instruct Different?
GPT-3.5 Turbo Instruct builds upon the successes of its predecessors while introducing notable advancements. One key difference is its enhanced ability to understand and execute instructions. GPT-3.5 Turbo Instruct has been fine-tuned to better comprehend and follow user instructions, resulting in more accurate and contextually appropriate outputs. Another improvement in GPT-3.5 Turbo Instruct is its increased efficiency. Despite the significant increase in parameters, OpenAI has optimized the model to provide faster response times, reducing the waiting period for users. This improvement is crucial for real-time applications where quick responses are essential. Additionally, GPT-3.5 Turbo Instruct exhibits an impressive level of versatility.
Use Cases for GPT-3.5 Turbo Instruct
The applications of GPT-3.5 Turbo Instruct are vast and varied, spanning multiple industries. One prominent use case is in the field of software development. Developers can harness the power of GPT-3.5 Turbo Instruct to generate code snippets, debug programs, or even build entire applications. The model’s ability to understand and follow instructions makes it a valuable asset for developers seeking efficient and reliable coding assistance. Another area where GPT-3.5 Turbo Instruct shines is in the realm of content creation.
Whether it’s writing blog articles, drafting marketing copy, or generating social media posts, the model can provide valuable assistance in generating high-quality content. Content creators can leverage GPT-3.5 Turbo Instruct to overcome writer’s block, generate creative ideas, or simply streamline their content creation process. Furthermore, GPT-3.5 Turbo Instruct can be utilized in the customer service industry. It can generate responses to customer inquiries, providing quick and accurate solutions. This can significantly enhance the efficiency of customer support teams and improve overall customer satisfaction. These are just a few examples of the countless possibilities that GPT-3.5 Turbo Instruct offers. Its versatility and ability to adapt to various domains make it a valuable tool for industries across the board.
Getting Started with GPT-3.5 Turbo Instruct
Getting started with GPT-3.5 Turbo Instruct is a straightforward process. OpenAI provides comprehensive documentation and resources to assist users in understanding and harnessing the model’s capabilities. The OpenAI API allows developers to integrate GPT-3.5 Turbo Instruct into their applications seamlessly. To begin, users need to sign up for the OpenAI platform and familiarize themselves with the API documentation. The documentation provides detailed instructions on how to set up the API, make requests, and handle responses.
OpenAI also offers various code examples and tutorials to help users get started quickly. Once the API is set up, users can experiment with different prompts and instructions to observe the model’s outputs. It is recommended to start with smaller, well-defined tasks to gain familiarity with the model and gradually explore more complex use cases. OpenAI’s developer community is vibrant and supportive, offering valuable insights, tips, and best practices. Engaging with the community can provide additional guidance and inspiration for utilizing GPT-3.5 Turbo Instruct effectively. By following the provided resources, users can embark on their journey with GPT-3.5 Turbo Instruct confidently and unlock its vast potential.
Examples of Successful Implementations of GPT-3.5 Turbo Instruct
GPT-3.5 Turbo Instruct has already proven its worth through successful implementations across various domains. One notable example is in the field of education. The model has been utilized to generate interactive and dynamic learning materials, providing students with personalized and engaging content. By tailoring the generated content to individual learning styles and preferences, GPT-3.5 Turbo Instruct enhances the learning experience and promotes knowledge retention.
Another application of GPT-3.5 Turbo Instruct is in the realm of chatbots and virtual assistants. By leveraging the model’s language generation capabilities, developers have created conversational agents that can hold more natural and human-like conversations. These chatbots can assist users in tasks such as making reservations, answering inquiries, and providing recommendations, offering a seamless and efficient user experience.
Furthermore, GPT-3.5 Turbo Instruct has been employed in the healthcare industry to generate medical reports and assist in diagnostics. By understanding medical instructions and generating accurate reports, the model reduces the burden on healthcare professionals and enhances the speed and accuracy of diagnoses. These examples highlight the versatility and potential of GPT-3.5 Turbo Instruct in transforming various industries. As the technology continues to evolve, we can expect to witness even more innovative implementations in the future.
Exploring the Future of AI and GPT-3.5 Turbo Instruct
GPT-3.5 Turbo Instruct represents a significant milestone in the advancement of AI, but it is just the beginning. As technology continues to evolve, we can expect even more powerful and sophisticated models to emerge. The future of AI holds the promise of even more seamless integration with our daily lives, enabling us to accomplish tasks more efficiently and effortlessly. With GPT-3.5 Turbo Instruct, OpenAI has showcased the incredible potential of AI models that can understand and execute complex instructions. This opens up a world of possibilities for applications in industries such as education, healthcare, customer service, and content creation. As researchers and developers continue to push the boundaries of AI, we can anticipate further breakthroughs that will reshape the way we interact with technology.
Ethical Considerations when Using GPT-3.5 Turbo Instruct As with any powerful technology, ethical considerations are crucial when utilizing GPT-3.5 Turbo Instruct. It is essential to ensure responsible and ethical use to avoid potential pitfalls and challenges. One primary concern is the potential for biased or unethical content generation. GPT-3.5 Turbo Instruct relies on the data it has been trained on, which can introduce biases present in the training data. It is important to carefully review and mitigate any biases that may arise in the generated content, especially in sensitive domains.
Another ethical consideration is the responsible handling of user data. As users interact with GPT-3.5 Turbo Instruct, data is collected and processed. It is crucial to prioritize user privacy and data security, ensuring that user information is handled by relevant laws and regulations. OpenAI has been proactive in addressing these ethical concerns and has implemented safety mitigations to prevent misuse of the technology. However, it is the responsibility of users and developers to exercise caution and uphold ethical standards when working with GPT-3.5 Turbo Instruct.
Final Thoughts
OpenAI’s release of GPT-3.5 Turbo Instruct marks a significant milestone in the field of AI. The model’s advanced language generation capabilities and enhanced ability to understand instructions open up a world of possibilities for various industries. From software development to content creation, customer service to education, GPT-3.5 Turbo Instruct offers versatile and powerful solutions. As with any transformative technology, it is important to recognize the benefits and limitations of GPT-3.5 Turbo Instruct.
By understanding its capabilities and ethical considerations, users can leverage the model responsibly and effectively. The future of AI is filled with exciting possibilities, and GPT-3.5 Turbo Instruct is just the tip of the iceberg. As researchers and developers continue to push the boundaries, we can anticipate even more advanced and sophisticated AI models that will shape the way we interact with technology. It is an exciting time for AI, and GPT-3.5 Turbo Instruct is leading the way towards a more intelligent and intuitive future.
Tech
A Closer Look at Apple’s iPhone 15 and iPhone 15 Plus

When it comes to smartphones, Apple has always been at the forefront of innovation. The iPhone series has consistently set the benchmark for what a premium smartphone should be. With the recent release of the iPhone 15 and iPhone 15 Plus, Apple continues to push the boundaries of technology and design. In this article, we will take a closer look at these two new devices and explore their key features, specifications, and more.
Features and Specifications
The iPhone 15 Plus takes the already impressive features of the iPhone 15 to the next level. One of the standout features of the iPhone 15 Plus is its larger display. It comes with a massive 6.7-inch Super Retina XDR OLED display, offering an immersive viewing experience. The display also supports ProMotion technology, which provides a smooth scrolling experience and adaptive refresh rates.
Under the hood, the iPhone 15 Plus is powered by the same A15 Bionic chip found in the iPhone 15. This ensures that the device can handle even the most demanding tasks effortlessly. Whether you’re editing videos, playing graphics-intensive games, or multitasking, the iPhone 15 Plus delivers exceptional performance.
The camera system on the iPhone 15 Plus is another area where it shines. It features a triple-camera setup with wide, ultra-wide, and telephoto lenses. This allows for greater versatility when it comes to photography, with the ability to capture stunning wide-angle shots or zoom in for detailed close-ups. The enhanced Night mode on the iPhone 15 Plus further improves low-light photography, capturing more detail and reducing noise.
Design and Display
Apple has always been synonymous with sleek and elegant design, and the iPhone 15 and iPhone 15 Plus are no exception. Both devices feature a glass front and back, with a stainless steel frame. The glass back allows for wireless charging, making it convenient for users who prefer to charge their devices wirelessly.
The display on both devices is truly stunning. The iPhone 15 features a 6.1-inch Super Retina XDR OLED display, while the iPhone 15 Plus comes with a larger 6.7-inch display. Both displays offer vibrant colors, deep blacks, and excellent contrast, making everything on the screen look incredibly sharp and vivid.
Camera Capabilities
Apple has always been known for its exceptional camera capabilities, and the iPhone 15 and iPhone 15 Plus are no exception. Both devices feature a dual-camera setup with wide and ultra-wide lenses, allowing users to capture a wide range of shots. The 12-megapixel sensors, combined with the new sensor-shift optical image stabilization, ensure that photos are sharp and steady, even in low-light conditions.
The Night mode on both devices has also been improved, allowing for better low-light photography. Whether you’re capturing a night skyline or a dimly lit room, the iPhone 15 and iPhone 15 Plus can produce stunning photos with enhanced detail and reduced noise.
Performance and Battery life
When it comes to performance, the iPhone 15 and iPhone 15 Plus are in a league of their own. Both devices are powered by the A15 Bionic chip, which delivers industry-leading performance and efficiency. Whether you’re running multiple apps simultaneously, editing videos, or playing graphics-intensive games, the iPhone 15 and iPhone 15 Plus can handle it all with ease.
Battery life is another area where these devices excel. The iPhone 15 features a larger battery compared to its predecessors, providing all-day battery life. The iPhone 15 Plus, with its larger size, offers an even longer battery life, ensuring that you can go through the day without worrying about running out of power.
Software and Operating System
The iPhone 15 and iPhone 15 Plus come with the latest version of iOS, Apple’s operating system. iOS offers a seamless and intuitive user experience, with a host of features and enhancements. From the redesigned Control Center to the improved Siri, iOS on the iPhone 15 and iPhone 15 Plus takes user interaction to a whole new level.
Additionally, both devices support the latest software updates from Apple, ensuring that you have access to the latest features and security enhancements. With regular software updates, you can rest assured that your device will continue to perform optimally and remain secure.
Pricing and Availability
The iPhone 15 and iPhone 15 Plus are available in various storage capacities to suit different user needs. The pricing of these devices varies depending on the storage capacity and the region in which you are purchasing them. It is recommended to check Apple’s official website or visit an authorized retailer for the most up-to-date pricing information.
As for availability, Apple typically releases its new devices in a phased manner, with different regions getting access to the devices at different times. It is advisable to check Apple’s website or contact your local Apple store for information on availability in your region.
Final Thoughts
The iPhone 15 and iPhone 15 Plus are a testament to Apple’s commitment to innovation and excellence. With their impressive features, stunning displays, powerful performance, and exceptional camera capabilities, these devices are sure to impress even the most discerning users.
Whether you’re a professional photographer looking for a portable camera solution or a power user who needs a device that can handle demanding tasks, the iPhone 15 and iPhone 15 Plus deliver on all fronts. With their sleek design, intuitive software, and long battery life, they are truly the epitome of a premium smartphone.
If you’re in the market for a new smartphone that offers the best of what technology has to offer, look no further than the iPhone 15 and iPhone 15 Plus. Visit Apple’s official website or your local Apple store to learn more about these incredible devices and make your purchase today.
-

 Sports7 days ago
Sports7 days agoOfficial: Juventus announces sixth purchase
-

 Health & Society7 days ago
Health & Society7 days agoThe intoxicated society
-
 Politics5 days ago
Politics5 days agoThe Russian patriarch to Putin: You are the first truly Orthodox president
-

 Sports6 days ago
Sports6 days agoBeautiful Juve: Vlahovic and youth rout Verona. Thiago Motta first
-

 Sports6 days ago
Sports6 days agoJuventus, Vlahovic: “Now we play a different game.”
-

 Politics4 days ago
Politics4 days agoEU Intensifies Pressure: Six-Month Extension of Russia Sanctions
-

 Health & Society3 days ago
Health & Society3 days ago7 Superfoods That Will Boost Your Fitness Results
-

 EU & the World5 days ago
EU & the World5 days agoBrittany Cartwright Files for Divorce From Jax Taylor After 5 Years of Marriage









